Slay the "Zero to MRR" Tax with Flowtriq's Lightning-Fast DDoS Defense
Picture this: it’s 3:00 AM on a Saturday. You’re finally hitting that deep sleep cycle when your phone explodes with PagerDuty alerts. Your SaaS platform’s latency is spiking, your database is gasping for air, and your "First Customer" success story is quickly turning into a churn nightmare because a botnet decided your origin IP looked tasty. This is the "Zero to MRR" tax—the moment your growth makes you a target.
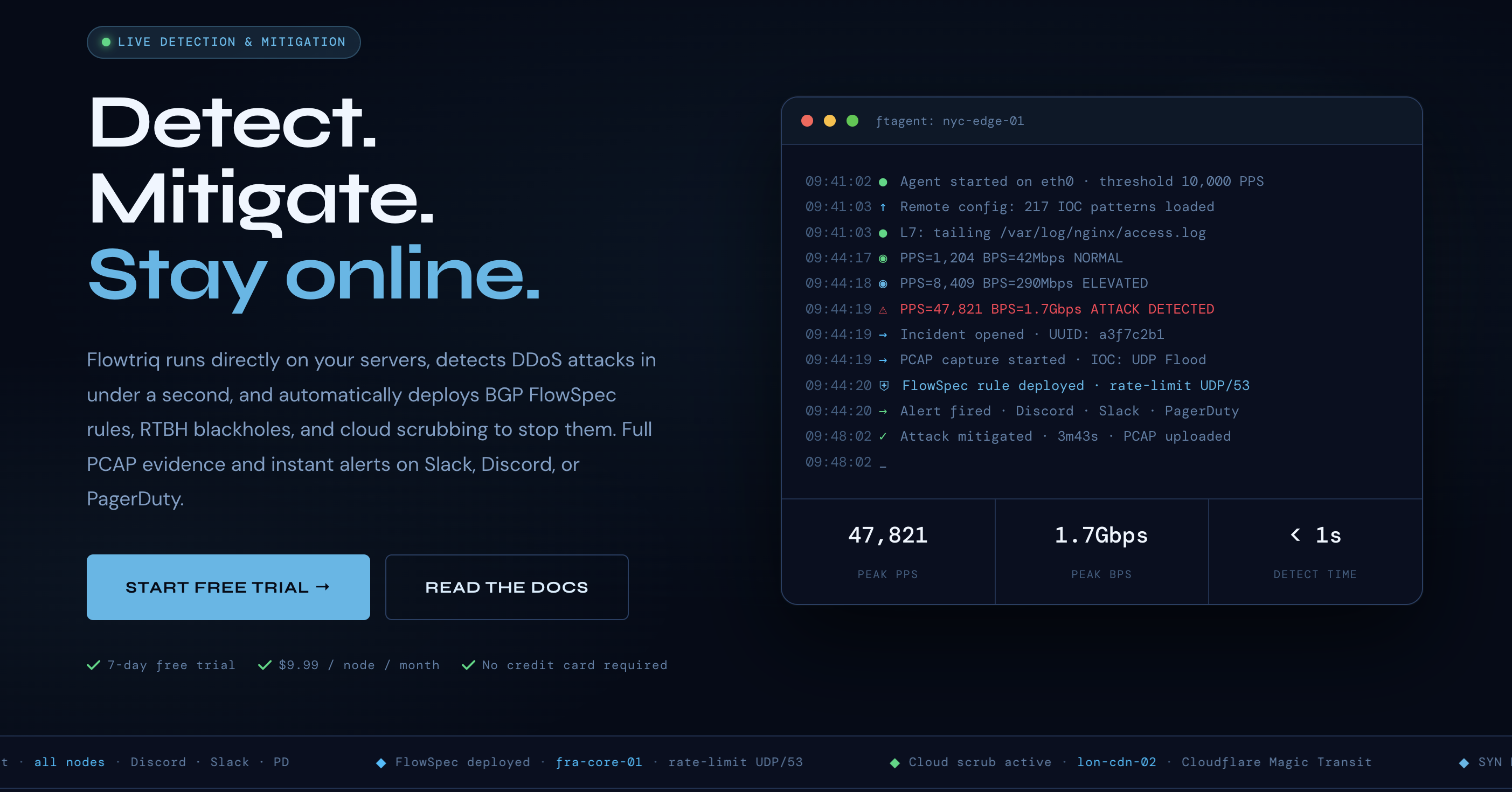
Flowtriq is a lightweight, agent-based DDoS detection and auto-mitigation platform designed to kill this scenario before you even wake up. Built on a philosophy of "install and forget," it utilizes a Python-based agent (ftagent) that sits directly on your Linux nodes. Unlike legacy hardware appliances that cost a kidney, Flowtriq focuses on sub-second packet-level inspection and automated BGP FlowSpec orchestration. It’s built for the bootstrapper who needs enterprise-grade shielding without the enterprise-grade complexity.
-- The "Zero-Trust" Packet Inspection Architecture --
Flowtriq’s architecture is a masterclass in decentralized edge security. Instead of routing all your precious traffic through a centralized scrubbing center (which adds latency and costs a fortune in bandwidth), Flowtriq moves the "brain" to your server. The ftagent hooks directly into the Network Interface Card (NIC), reading packets in real-time.
The design philosophy here is "Local Detection, Global Orchestration." The agent handles the heavy lifting of PPS (Packets Per Second) monitoring and anomaly detection using dynamic baseline learning. This data is then synced to the Flowtriq cloud dashboard for multi-node management. By avoiding a "middle-man" proxy for initial detection, Flowtriq achieves a sub-1-second mitigation trigger. When an attack is detected, the platform doesn't just scream for help; it pushes BGP FlowSpec rules or RTBH (Remote Triggered Black Hole) instructions to your upstream providers (like OVH, Hetzner, or Cloudflare Magic Transit) to drop the malicious traffic at the edge.
-- Breaking Down the Mitigation Engine --
> Core Capabilities
- *Sub-Second Multi-Vector Defense: Flowtriq doesn't just look for "high traffic." It classifies over 8 attack types, including SYN floods and complex Layer 7 application attacks. For a SaaS founder, this means the system can distinguish between a viral marketing spike and a Memcached amplification attack.
- *IOC Pattern Matching: With a library of 642,000+ Indicators of Compromise (IOCs), the platform cross-references incoming traffic against known Mirai botnet variants. It’s like having a digital bouncer who recognizes every known troublemaker in the world.
- *Automated Incident Runbooks: You can chain mitigation steps. For instance, Step 1: Trigger local
iptablesrules. Step 2: If traffic exceeds 1Gbps, announce BGP FlowSpec to the upstream provider. This prevents "over-mitigation" where you accidentally block legitimate users while trying to stop a small bot.
> The Integration Ecosystem
Flowtriq is built for the modern DevOps stack. Its alerting system isn't just an afterthought; it fires within one second to Discord, Slack, PagerDuty, and OpsGenie. For those of us building custom internal tools, the webhooks and API allow you to trigger custom workflows—like spinning up extra capacity or putting your site into "Under Attack" mode automatically. The integration with major infrastructure providers like Cloudflare and Hetzner ensures that your mitigation is as global as your traffic.
> Security & Compliance
Data handling is a major concern when you're installing agents on production boxes. Flowtriq maintains an immutable audit log of every action taken—essential for compliance audits or explaining a downtime event to stakeholders. For enterprise users, they offer 365-day PCAP (Packet Capture) retention, allowing for deep forensic analysis of attacks long after the dust has settled. Their original research, including the Mirai kill switch (CVE-2024-45163), proves they aren't just selling a UI; they are active participants in the threat intel community.
-- Performance: Light Enough for a Raspberry Pi --
Because the ftagent is written in Python and optimized for Linux, the resource overhead is negligible. It’s designed to run on everything from a massive bare-metal server to a tiny edge node. In my experience, the "resource tax" of security tools often kills the ROI for small startups, but Flowtriq’s flat $9.99/node pricing means you aren't penalized for your traffic volume. You get the same sub-second detection whether you're pushing 10Mbps or 10Gbps.
-- Technical Alternatives in the Wild --
In the journey from zero to MRR, you’ll encounter several ways to skin the security cat. If you're looking for a CDN-first approach, you might look at Cloudflare, but that often requires moving your entire DNS and can get pricey with their advanced WAF features. For those who want more manual control over their network stack, I'd suggest checking out my deep dives on other infrastructure-heavy tools.
While Flowtriq excels at the agent-to-edge level, you might also consider how it fits alongside your existing stack. If you are comparing different approaches to infrastructure security, take a look at our analysis of specialized tools like Cloudflare for edge caching or Fastly if you're doing heavy logic at the edge. Flowtriq is the "special forces" unit you bring in specifically to stop the network-level bleeding.
-- The Developer Experience --
The "two-minute install" isn't marketing fluff. The CLI-based setup is clean, and the dashboard provides a "single pane of glass" for multi-node environments. I’m a huge fan of their free tools—the BGP FlowSpec builder and live DDoS attack map are actually useful resources, not just lead magnets. The documentation is written by engineers for engineers, skipping the fluff and getting straight to the iptables generators and PCAP analyzers.
-- The Technical Verdict: Is It Worth It? --
Flowtriq is a "no-brainer" for anyone running their own Linux-based infrastructure, especially game server hosts or SaaS companies with high-visibility origin IPs.
Strengths: Unbeatable price-to-performance ratio, sub-second detection, and zero traffic surcharges. The automated PCAP capture is a godsend for post-mortem reports. Limitations: It requires comfort with the Linux CLI and managing your own nodes. If you're 100% serverless on Vercel or Netlify, this isn't for you. Ideal Use Case: Scaling startups that have outgrown basic "free tier" protection and need to ensure 99.9% uptime against sophisticated network-layer threats. It’s the insurance policy that actually does the work for you.
EXTERNAL TRANSACTION:
VISIT FLOWTRIQ -->